#10 - CrimeOps: How the Conti leaks exposed the structure of the cybercrime organisation
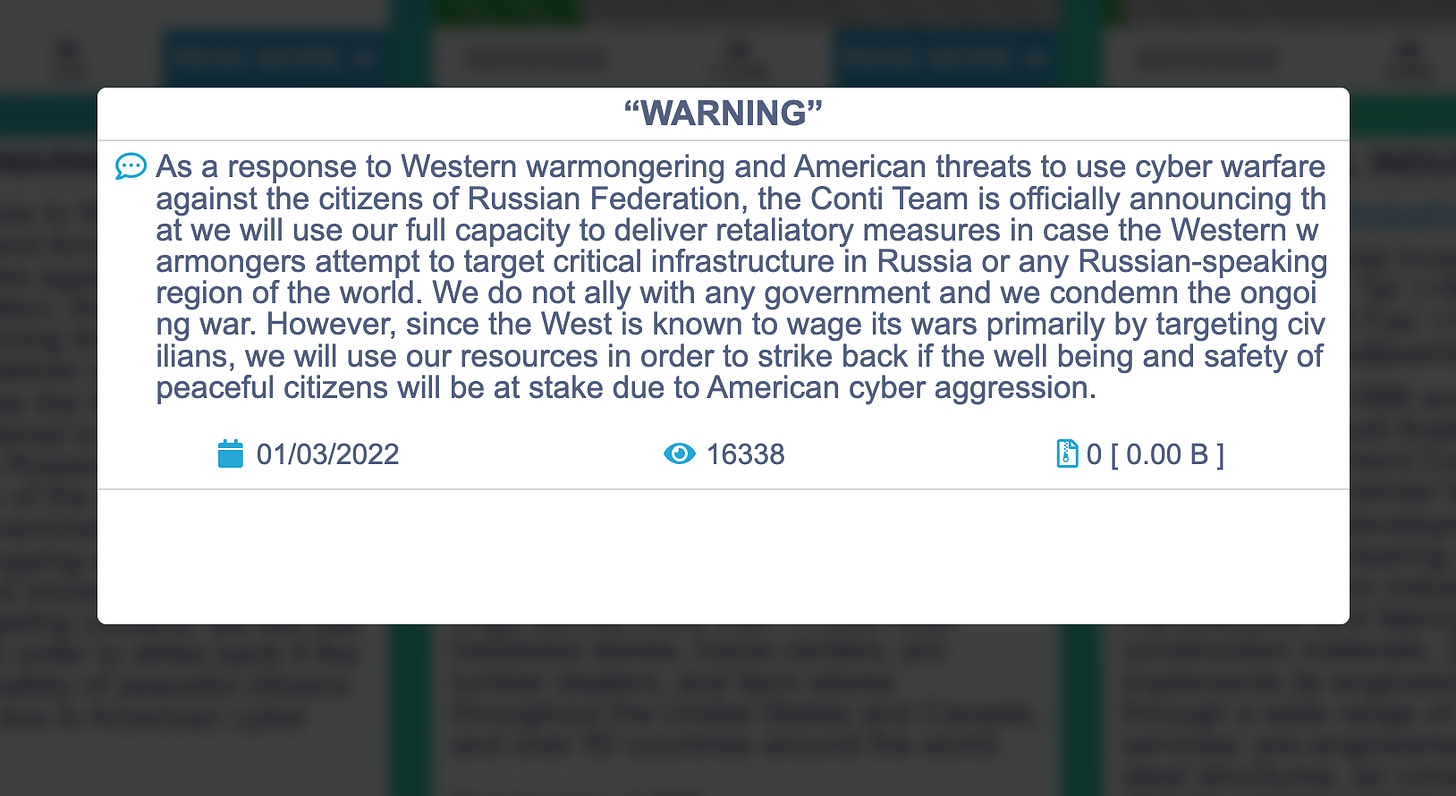
Conti is, according to virtual currency tracking firm Chainalysis the most significant ransomware strain by revenue in 2021, extorting $180 million from victims. In response to the invasion of Ukraine, they announced it would fully support Russian Federation against Western cyberwarfare.
On February 27th, the Twitter account “Contileaks” started posting links to the messages taken from Conti’s private chat application. It is not clear who posts the messages. Some early rumors pointed to a Ukrainian member of the gang who did not share their peers’ manifest, but now it seems the leaker is a security researcher from Ukraine who compromised them.
The chats reveal how the Conti group organizes itself and its hierarchy. They follow the structure of many legitimate IT medium-size organizations. In the conversations, we can learn that they have between 65 to 100 employees with salaries ranging from $2000 to $10000 in Bitcoin. And this is one of the reasons for their success: the secret is their operational art of cybercrime: they are masters of the CrimeOps.
They organize the departments with their own budgets, staff schedules, sprints (yes, Conti is an Agile organization), and goals. We can infer the following departments:
Leadership Team: A small group of leaders manages the different business units. They also track how the team members perform the assigned tasks with the quality needed.
Human Resources: Like any other tech company, they struggle with turnover, lack of tech workers, and rival gangs hiring their talent. They have a budget to publish ads in Russian-speaking legal job forums and hack forums. They also deal with complaints about the managers, working hours, burnout, and work-life balance.
Product: Coders, testers, product managers write the different malicious “products” and verify that security tools don’t detect them.
IT Operations: Keep the lights on the infrastructure to permit 24/7 attacks.
R&D: Reverse engineer different commercial products to find vulnerabilities to exploit.
Sales: Find new companies suitable to “use” (extort) their products
The only team I cannot identify in a classic IT shop is in charge of offensive activities to distribute the ransomware and steal data. They even outsource activities they consider of low value for the business, like email spamming.
But what makes Conti the best ransomware CrimeOps organization is how they excel in creating an engine to seek and target the right companies to extort. The flow of new ransomware victims is constant. They run a repeatable business process that scales (well, sort of). They need to find information about potential targets and tools like ZoomInfo or paid subscriptions to Crunchbase help them to target the right companies, just like any Sales team would do.
Scaling is an issue. The leaders ask the frontline workers to be more professional and let them know that a mistake can impact the revenue and the employee salaries. Frontline workers handle an enormous infrastructure. They target thousands of PCs and servers, so they often lose control of bots and platforms simply due to human mistakes. Does this pain sound familiar to anybody working in a scaleup?
As with any other scaleup, Conti is struggling with a widespread problem in high-growth businesses. Besides, Conti is not a legitimate business and faces particular challenges. For example, they need to use industry tools and services, but it is not easy for criminal organizations to buy these products. They have access to tools like Cobalstrike, VMWare Carbon Black, and others through intermediaries.
A company with $180M yearly revenue with almost triple-digit growth year-over-year and less than 100 employees would be a massive success with a multi-billion valuation -applying the calculations for a tech scaleup of the West. But I’m using my Westerner mentality, and that’s the main problem when analyzing cybercrime organizations. Still, it’s hard to grasp how it is possible to keep such a large organization under the cover for such a long time. But that’s for another newsletter.
In this Github repo, you can learn more about the Conti Leaks chats in English.
If you want to dig into the rabbit hole, you can learn about the connections between Ryuk and Conti.
An interesting thread in Twitter with a deep analysis of the chats in English.
The Music Snippet
Seek and Destroy!