#11 - The weeks that changed my professional career
One of the things I like most about being an engineer is meeting interesting people from all over the world. Brilliant people from whom you can learn a lot. People of different cultures, education, and motivations. With varying life paths that by chance of fate cross in your life.
Although we are all equal, being born and growing up in Madrid is not the same as in Shanghai, Los Angeles, or Kyiv. Our culture and traditions deeply condition our personality, and of course, it also influences our professional development. Professionals from Western Europe share similar values. And we tend to apply our moral filter in our relationships, often with arrogance. Or unconscious bias.
A few years ago, I had a professional experience with a relevant company in a former Soviet republic that helped open my eyes. I will not name the company because, to the eyes of a Westerner, what they did was illegal, or at least immoral.
During Christmas 2015, we suffered continuous attacks on my previous company's Cloud Computing platform. The type of attack was "synthetic account creation abuse": a malicious actor created hundreds of test accounts and then used the virtual machines without paying for them. He used anonymous proxies to hide his identity, and although we detected and blocked the attacks, they kept coming back relentlessly.
We decided to investigate: what were they using those virtual machines for?. We were amazed to discover that they used a popular Infrastructure as Code tool to deploy specific applications that stressed the platform. However, it did not look like they were trying to target other platforms or establish connections indiscriminately. They were “testing” some stuff in our platform at a large scale.
When we started analyzing the source connections of the Infrastructure as Code tool, we found out that the IP address was not anonymized and that it was always the same. Searching through the IP addresses of connections over the last weeks, we found the IP address in a legitimate account on our platform. It was created with an email from a famous tech company in a former Soviet republic. We even managed to get his Linkedin profile, and he turned out to be an engineer of that company.
First, I wrote to the account's email with the whole collection of evidence about his activity attached, reminding him that in addition to a violation of the Terms of Service, he could be committing a crime of Computer Sabotage. I received no reply, and the attacks continued. I also contacted him through Linkedin, but nothing. No response. Then I wrote to the CEO (did I mention we were introduced a few years earlier at World Hosting Days?). Nothing. But the attacks carried on.
I was desperate, and I did not know what to do. The preemptive countermeasures could limit the attacks, but it was costly, and the abuse came from a legit company that made millions. It was not a script kiddie from a basement in Montana!
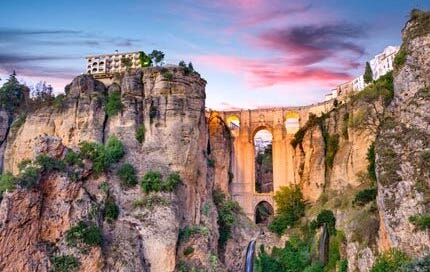
I started to investigate the company to contact an investor, advisor, or someone who would listen to me. By chance, I found out they had a subsidiary company in Málaga. And then it became clear to me: I would threaten them with a lawsuit for Computer Sabotage (Sabotaje Informático) to the Spanish branch. I had nothing to lose, but would it work?
After informing to the CEO by email that a legal action was going to take place against the Spanish subsidiary if they continued abusing the platform, the attacks stopped. And 24 hours later, the CEO answered my emails, apologizing for any inconvenience during the former weeks.
In the post-mortem analysis of the crisis, we concluded that the abuse of the platform was a deliberate way to save a few thousand dollars and that it was something that the company was aware of and probably even encouraged. But why would a company that earns millions of dollars and makes a profit do something like this? Well, they were just doing business. That’s all. They did not want to screw up us; they just didn’t care. Did they know their actions cost us time and resources? Sure. But probably they felt it was our problem, not their business.
From the Westerner mindset, they should have a culture in the company to discourage and penalize whoever tries to perform any shady action. But from their perspective, it’s not their business what could happen to us if they decided to create thousands of synthetic accounts and abuse our trial period. Worse, trying to solve the problem using a backchannel and being diplomatic only exposed that I was "soft." The balance changed when they realized they could face a lawsuit in an EU country.
In a globalized world it’s very arrogant thinking of us as the only “right” way of doing business, because there is no such a thing. And I was not ready to handle a situation where my counterparts had very different business ethics.
I learned a lot during those crazy weeks. And I was lucky enough to get started in the world of online abuse. You see, a shady engineer with plenty of spare time and a willingness to save his company some bucks made me change my area of expertise.
The Music Snippet
Jane’s Addiction is always a win-win