#13 - Does security really matter?
In three months, a relatively new cybercrime gang named LAPSUS$ claimed to have successfully breached major firms like Microsoft, NVIDIA, and LG. But this week, the group released screenshots of the administration panel of the Identity Management company Okta. Since Okta provides an enterprise-grade single sign-on service allowing their employees to log in to multiple systems with a shared authentication step, this potential breach could have severe implications for customers.
In 2019 Auth0 acquihired my company Apility.io. At that time, Auth0 was one of the most important (if not the most) competitors of Okta in the Identity Management business. Incidentally, the day after I left the company in 2021, Okta acquired (or merged with?) Auth0, creating the most extensive offering in the industry. When I was in the company, I learned how critical security was for them and how all of us knew that if a bad actor hacked the company and gained access to our users’ database, we would be dead. But the events of the week say something different. What is going on?
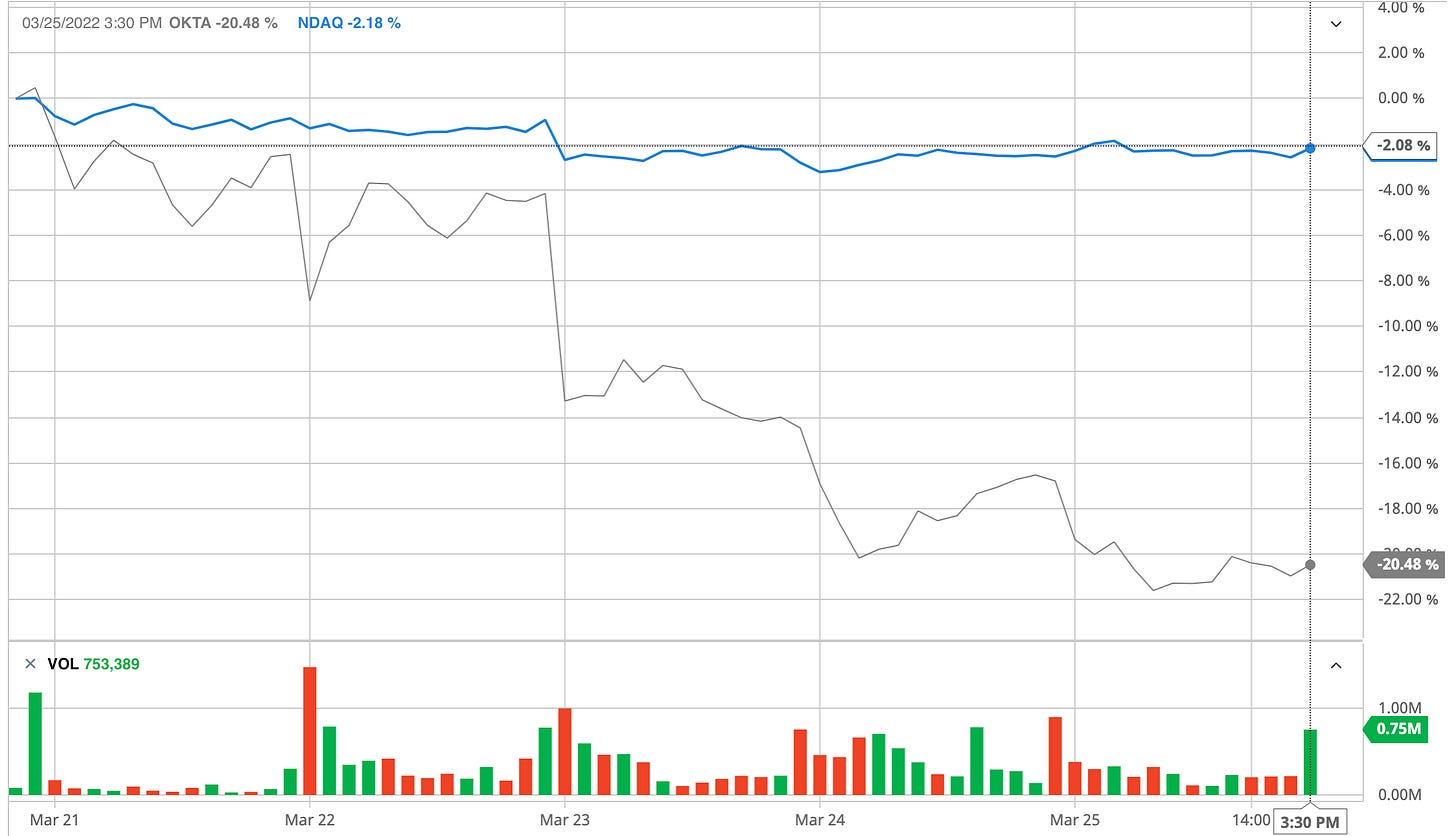
The users’ database of Okta was never compromised, but nobody was quite sure during the first 24 hours after the announcement in the Telegram group of LAPSUS$. Surprisingly, if you look at the chart above comparing the OKTA stock with the NASDAQ index, there was a 4.25% fall. No selling panic, just a simple correction.
A quick note here: I don’t know much about Okta’s internal architecture. I had a lot of curiosity during my time at Auth0, and I had the chance to learn about their internals thanks to random conversations with Okta ex-workers. Still, I don’t think the breach impacted Auth0’s platform; you cannot merge such complex platforms in one year!
So after the first hours of madness, some information started to pour about what happened: the laptop of a subcontractor was compromised, and the criminals were able to take screenshots of the administration tools of the Customer Support Center. The screenshots showed factual information of several users, but LAPSUS$ never really gained control of that tools or escalated privileged access. The security crisis could end here, but then the Public Relations crisis exploded.
With shock and awe, we all discovered that the breach happened in January, but they neglected to communicate to the affected customers because they didn’t know what had happened until this week. They were not diligent enough about closing the case promptly. Two months in cybersecurity is an eternity (please ask experienced CISOs and SOCs workers how many nights without sleep in their careers doing forensics). Also, the flow of information showed an incomplete picture, and when they tried to provide more details, they created more confusion. The communication chaos brought a more abrupt fall in the stock value than the announce of the breach in itself.
So my point here is: it seems more important to display a sense of security and communicate that you have under control all scenarios than being a natural-born zero-trust (paranoid-level) company like Okta that fails to explain what happened. Security becomes psychological insurance that companies are willing to pay for it. If companies do security, so other people see them doing security, your efforts have to be visible, not necessarily effective.
Several examples of companies justify my opinion: they only need to spend enough to show they are doing something, but there are few consequences when they screw up (Solarwinds, for example). And it is going worse. If new incidents dilute the others to the point that no one cares, nobody will ever care about implementing good security, but only bragging about it.
The Music Snippet
Today the drummer of Foo Fighters, Taylor Hawkins, passed away. Rest in Peace. What a sad coincidence, I had chosen this song for the music snippet two days ago.