#6 - Beijing2022 Olympics app spyware, IBM Watson fiasco, and another massive Ethereum hack.
Is the Beijing2022 Olympics app spyware?
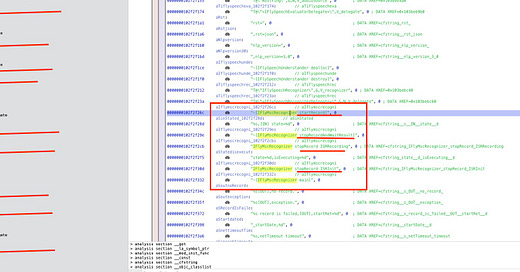
The spyware researcher and Ph.D. student Jonathan Scott published a Twitter thread pointing at the Official Beijing2022 Olympics App as spyware. He claims that the app can collect, analyze and save all Olympian audio on Chinese servers thanks to the technologies developed by iFlytek, a company banned in the US because of human rights violations against the Uighurs and Kazhaks minorities.
From the perspective of a westerner citizen, this comes as no surprise. It helps to boost the bias against the Chinese regime, and the mass media will buy this story without really questioning if it is true or not. And it happened when BBC journalist Ed Butler interviewed him on February 1st (the BBC deleted the tweet and the interview a couple of days later).
After posting the original tweet, the cybersecurity community raised its concerns about the accuracy of the problems discovered. Ranging from “we cannot affirm that the app is spyware” to “what the fuck are you talking about, asshole!”, it seems that Jonathan Scott spread fear and uncertainty over the app without a deep analysis of the code of the app and lack of objective evidence.
To summarize Jonathan’s concerns: They use an iFlytek library to record audio and multiple connections to servers hosted in China.
The library seems to be a voice assistant. So a user needs to talk to the app, and the app will record the voice to process it locally and send data and commands to servers hosted in mainland China. Think about Alexa or Siri, and you have the same kind of technology developed by a Chinese firm. Does it mean it records all conversations? No. Does the app send all the conversations to any server in China? We don’t know yet.
Regarding the connections to servers in China, I wonder if all Americans really think any digital service in the world has to connect to an AWS, Google, or Azure region in the US. Being an event in China sponsored by the Chinese government and supported by Chinese companies, they will obviously use their own technical infrastructure.
The last claim was some configuration flags in the app that could enable censorship when saying a list of taboo words. The technology from iFlytek can detect when somebody says forbidden words and can trigger actions. It looks like the hand of the Chinese government here, but again, does it mean this is spyware? No.
Jonathan Scott reversed the app’s code and performed a superficial and not in-depth analysis of the code, but technically savvy enough to deceive mass media and even specialized outlets, but not cybersecurity professionals. As the last example of bad practices, he mistook Dalvik bytecode as x86 code. In a community where reputation is everything, some members raised their concerns a long time ago.
The IBM Watson fiasco
IBM agreed to sell part of its IBM Watson Health business to private equity firm Francisco Partners. According to people familiar with the plans, the value of the assets is more than $1 billion.
IBM spent around $5 billion in acquisitions alone, plus the money invested in building products and services. IBM Watson Health had at one point 7,000 employees, which means that this was a total failure, and they needed just to cut their losses and move on.
Healthcare is one of the most significant parts of the economy. In the US, it’s a whopping three American trillion dollars business with legacy technology infrastructure where tech companies can earn a lot of money if they are successful. There’s a tremendous amount of data collected every day in the care of hundreds of millions of people, but nobody knows how to connect that data and extract valuable information. That’s the problem Watson wanted to fix but failed.
Does it mean that AI is not suitable for Healthcare problems? Not really. It seems that Healthcare is a sector that technology disruptors do not understand: being audacious when you’re dealing with people’s lives and health, you need to have evidence to probe that you can do what you say you can do.
$323M in Ethereum stolen
An attacker has exploited the Solana Wormhole bridge for close to $323 million in ETH. Wormhole is a bridging protocol that enables assets to move across various blockchain protocols. When a user sends assets from one chain to another, the bridge locks the assets and mints a wrapped version of the funds on the destination chain.
It resulted in the theft of 120k wETH, worth about $323 million at current prices. Etherscan transaction records detail the robbery of 93,000 of the exploited ETH. Researchers have explained how the attacker executed the exploit, one of the most considerable of a decentralized finance protocol to date.
Solana devs offered a $10 million bounty to the hackers in exchange for $320 million in stolen funds. The agreement would allow the hackers to keep the money without fear of prosecution. Last Thursday, Wormhole posted an update, saying that funds were restored, and the bridge was back online. However, the 120k wETH is still in the attacker’s wallet, so the Wormhole team probably secured the funds from their investors.
$320M is a large bug bounty to fix a vulnerability indeed.
More stuff
An annoyed hacker took down the whole North Korean internet.
Germany courts fined a company website for leaking users’ IP addresses to Google when using fonts online.
The music snippet
Trent Reznor and David Bowie’s I’m afraid of Americans…