#14 - What's wrong with Crypto Bridges
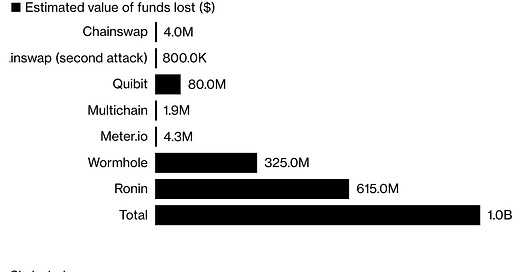
On March 23rd, an unknown actor hacked the Bridge chain of the Ronin Network that powers the game Axie Infinity resulting in a loss of 173,600 Ethereum and 25.5M USDC, equivalent to over $600M. This new hack adds to the recent $300M Wormhole hack incident and piles up to a whopping $1B in stolen crypto assets from Bridges in the year to date. The attack highlights how bridges are becoming the most profitable attack vector.
In plain English, Bridges are protocols that “wrap” tokens from one network to another. Tokens are digital assets defined and built on a specific blockchain. In the beginning, there was only the Bitcoin blockchain. Nowadays, there are thousands of blockchains, each with its purpose and particular value to users. Using a token of a specific blockchain in another is not possible, but some blockchains allow embedding code in themselves and run when predetermined conditions are met. In this case, these “smart contracts” are meant to function as a one-to-one representation of the value of other currencies (for the sake of simplicity, I’m oversimplifying a lot). A Bridge is where both Blockchains intertwine and exchange their tokens (or wrap a token in the other).
Attackers have realized Bridges are the weakest link in the supply chain of the Decentralized Finance (DeFi) world. But why are they so fragile? Let’s first see how the hack of the Ronin Network worked to understand the problem.
A Blockchain Bridge from Bitcoin to Ethereum could work this way:
Users pay a bridging fee and send several tokens X to a deposit address on the source blockchain (Bitcoin)
A validator locks the tokens. A validator can be a centralized custodian (BitGo) or a decentralized non-custodian like smart contracts.
The destination blockchain (Ethereum) is informed about the locked-up tokens.
A Y number of tokens equivalent to the X tokens in the source blockchain will be issued in the destination blockchain.
The new Y tokens are sent to a user’s destination address in the blockchain.
Centralized custodian validators are considered less secure than decentralized designs, which are safer and more robust by design. The Ronin Bridge was an in-between: not a centralized third-party custodian, but not a decentralized design using smart contracts.
The Ethereum sidechain created for Axie Infinity was hacked using an exploit. The Ronin chain currently consists of nine validator nodes. Five out of the nine validator signatures are needed to recognize a Deposit or a Withdrawal event. The attacker managed to get control over four Ronin Validators and a third-party validator run by Axie DAO.
According to their communication: “The validator key scheme is set up to be decentralized so that it limits an attack vector, similar to this one, but the attacker found a backdoor through our gas-free RPC node, which they abused to get the signature for the Axie DAO validator. This traces back to November 2021 when Sky Mavis requested help from the Axie DAO to distribute free transactions due to an immense user load. The Axie DAO allowlisted Sky Mavis to sign various transactions on its behalf. This was discontinued in December 2021, but the allowlist access was not revoked. “
One of the most surprising events of the hack is that it went unnoticed for almost a week, until a user tried to withdraw 5k ETH from the bridge and could not. To support the investigation of the incident, Binance said it had temporarily suspended withdrawals and deposits on the Ronin Network and blocked addresses by the potential hacker.



If the bridge has a centralized design, experts say that Validators are run by unaudited computer codes, making them vulnerable to bad actors. Moreover, the identities of validators/nodes, who run the transactions, are unknown. Also, the bridge was not a decentralized architecture; once the bad actors took control of five out of the nine validators, they had control of the transactions made. In previous bridge hacks, the root cause was a “smart contract” bug, an abuse or a coding mistake. But not this one, this is a classic hack of private keys in a multi-key setup.
If the bridge has a decentralized design, it cannot avoid potential issues due to mistakes, abuse or bugs in the code of the “smart contracts” that control the wrapping of the source tokens in the destination blockchain. Rolling back actions performed by the smart contracts are not part of the design of the blockchains, and as far as I know it’s not easy to implement as smart contracts. And this is a big challenge because it’s part of the nature of blockchain and smart contracts.
According to Vitalik Buterin, “it's always safer to hold Ethereum-native assets on Ethereum or Solana-native assets on Solana than it is to hold Ethereum-native assets on Solana or Solana-native assets on Ethereum.” I think this is why multichain ecosystems like Polkadot, which can support multiple blockchains, are really good alternatives in the future.
Thanks to the open design of the blockchains, we know where the stolen crypto is, and the exchanges will not allow the cybercriminals to convert it to other currency, crypto or not. I think a shady guy with a shady company it’s negotiating with the criminals to get those assets back for a hefty bounty.
The Music Snippet
We have a new record from Red Hot Chili Peppers, but this classic is perfect.